World Password Day — which falls on the first Thursday of May — was created to raise awareness about the critical need for good passwords.
Almost every two weeks someone on the Internet is screaming about their password getting leaked.
Breaches continue to happen on a massive scale as companies collect data on millions of people while failing to protect them properly.
But just because your information is stolen doesn’t mean that you’re helpless.
You can, and should, change your passwords.
I am a password leakage victim! What should I do?
When potential hackers have access to this massive amount of login data, they’re not sitting at a computer trying to log into every account one by one. They’re using bots to do it through a technique called credential stuffing, which automatically blasts multiple services with the same set of login information.
If you’ve reused those old passwords for different platforms, a potential hacker can use the leaked passwords to break into your newer accounts with these bots.
This means that you have to change ALL your passwords and further create different passwords for every platform you log into.
How can I create a really strong password?
First and foremost – don’t use any of the passwords from the list below. This is a list of the worst passwords from all over the world and the number of individuals who use them.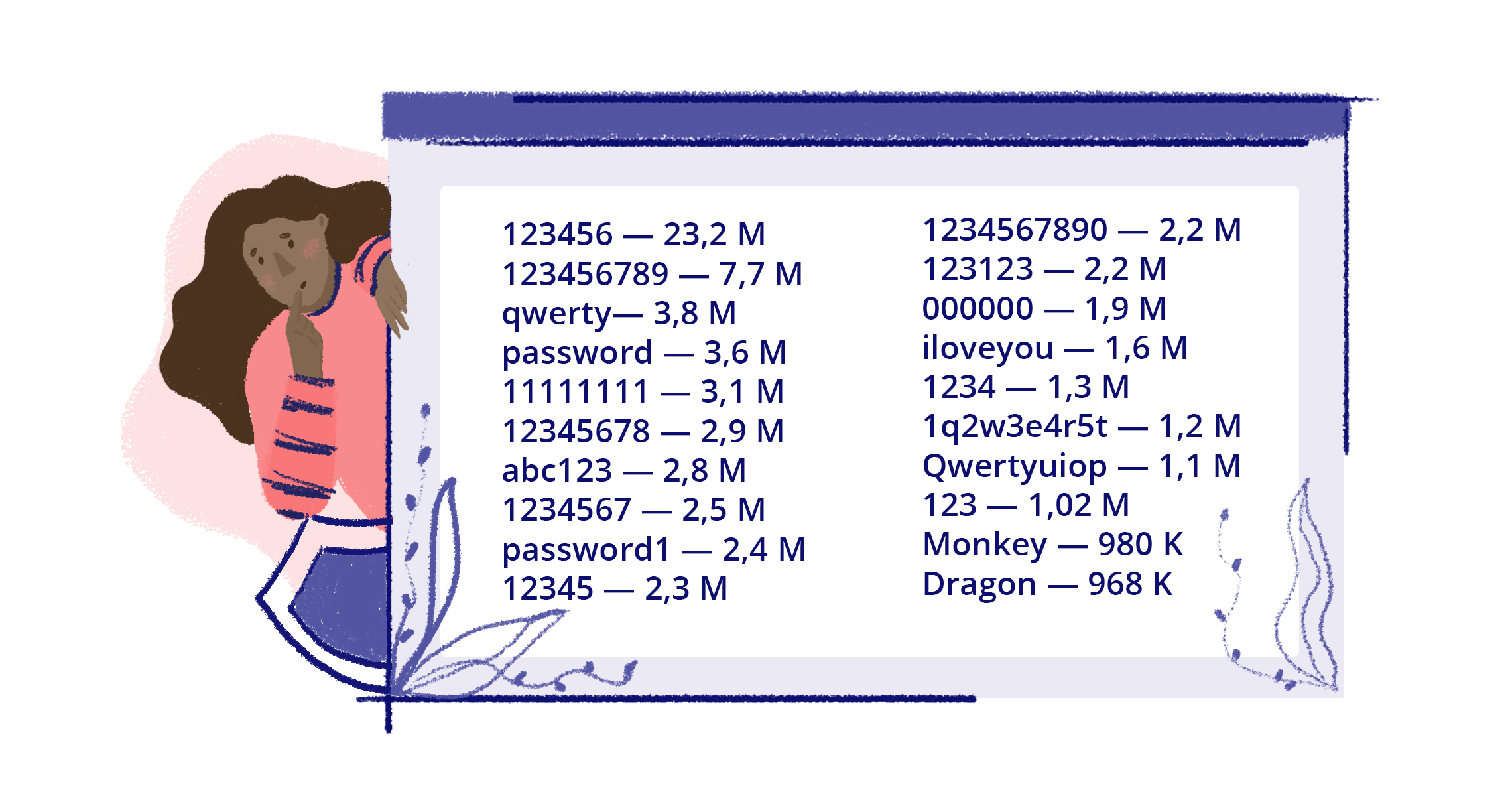
Make the password long. Try to choose nothing shorter than 15 characters.
Use a mix of characters. Fortunately, this is a common requirement for many websites. The more you mix up letters (upper-case and lower-case), numbers, and symbols, the more potent your password is, and the harder it is for a brute force attack to crack it.
Avoid common substitutions. Password crackers are hip to the usual substitutions. Whether you use DRAGONSTONE or DRAGON8377, a brute force attacker will crack it with equal ease.
Don’t use memorable keyboard paths. Much like the advice above to not to use sequential letters and numbers, do not use sequential keyboard paths either (like qwerty). These are among the first to be guessed.
And an additional piece of advice from PDFfiller – when dealing with document management platforms, pay critical attention to the security measures they provide.
- Two-factor authentication for e-signature identity verification and password-protected folders offers enhanced safeguards for sensitive data.
- Every document generated, edited, moved or shared should have a unique digital audit trail that records specific identifying information: IP address, geo coordinates, browser version, OS information and time stamp. PDFfiller’s audit trail ensures that each document is technically & legally sound.
- Compliance certifications and regulations – SOC 2 Type II certification, GDPR compliance, HIPAA compliance and PCI DSS certification will greatly reduce the risks of hacker and malware attacks, as well as password leakage.
Celebrate World Password Day the right way!